Malware analysis Malicious activity
Por um escritor misterioso
Last updated 22 outubro 2024

How to Do Malware Analysis?

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs
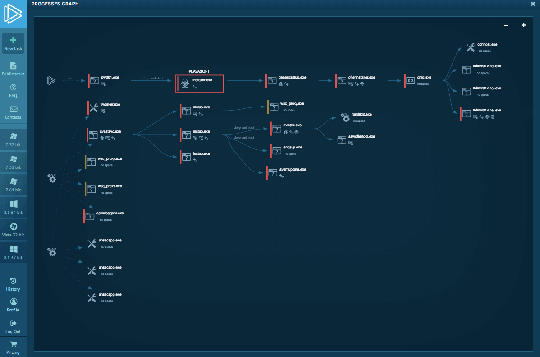
Interactive Online Malware Sandbox
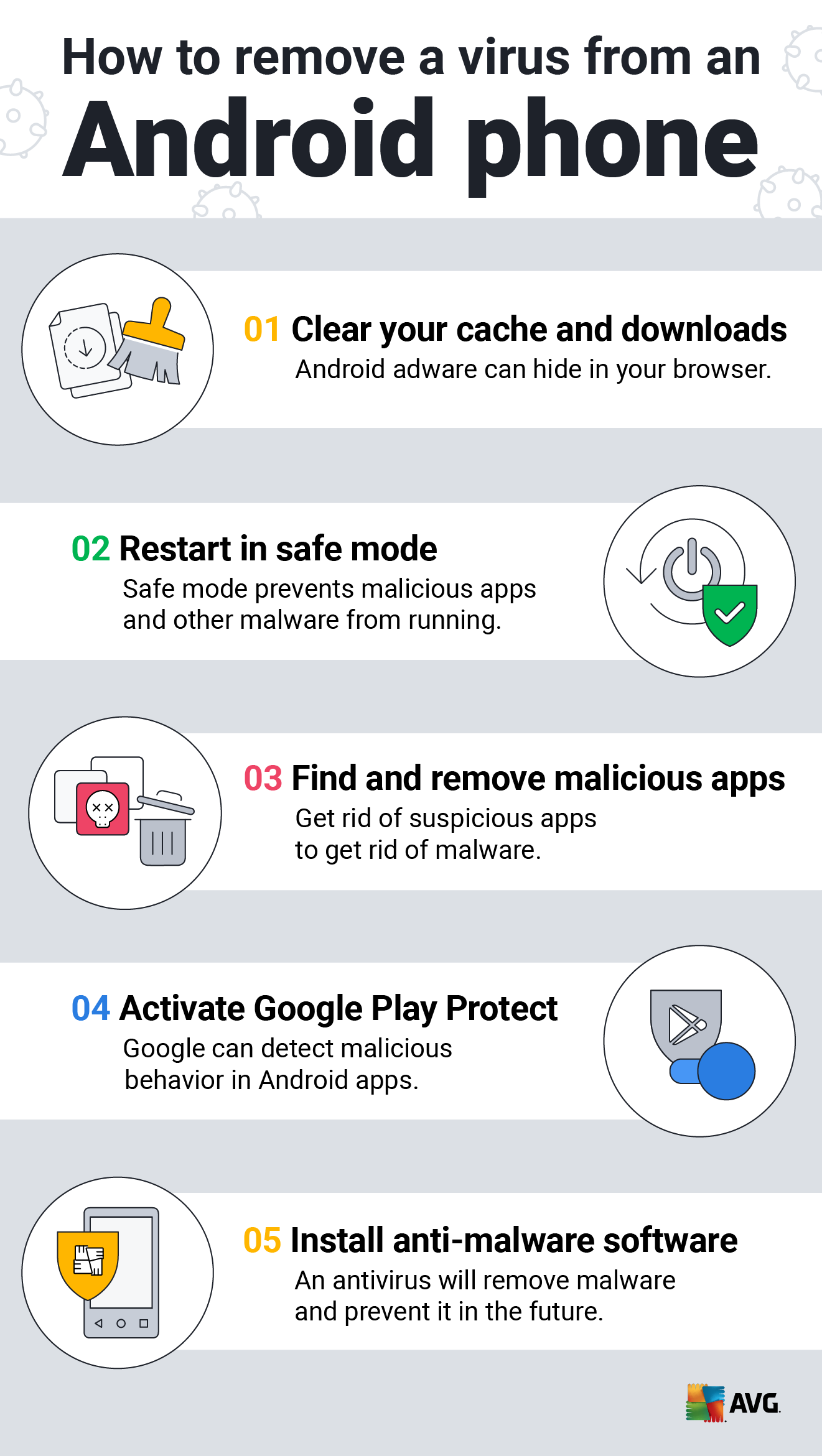
How to Clean an Android or iPhone from Viruses for Free

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Malware Analysis: Steps & Examples - CrowdStrike
Malware analysis Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware Analysis Framework v1.0

What is Malware? Definition, Types, Prevention - TechTarget

Malware Analysis Benefits Incident Response

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug

Mastering Malware Analysis
Recomendado para você
-
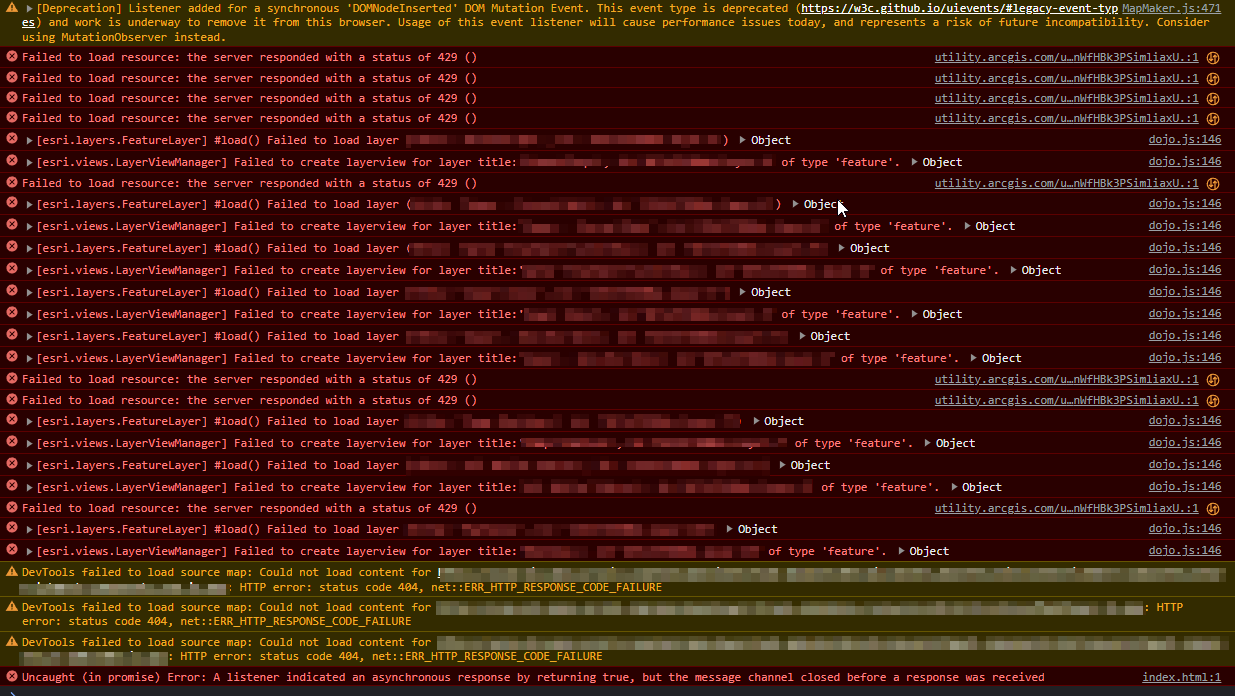
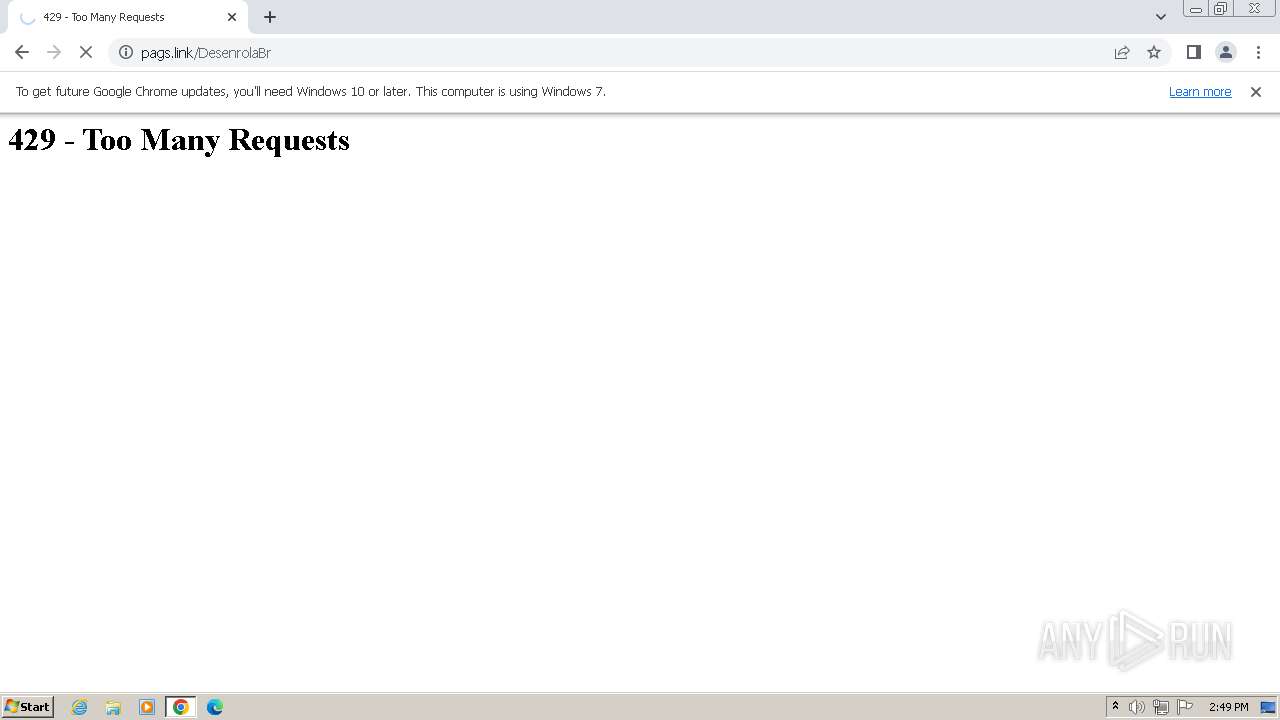
 HTTP Status Code 429: What Is the 429 Too Many Requests Error?22 outubro 2024
HTTP Status Code 429: What Is the 429 Too Many Requests Error?22 outubro 2024 -
 How to Fix Google Chrome Error Too Many Requests 429 In Windows22 outubro 2024
How to Fix Google Chrome Error Too Many Requests 429 In Windows22 outubro 2024 -
![Fix Chrome Too Many Requests 429 Error [Solved]](https://i.ytimg.com/vi/_kjTLMjZmtk/maxresdefault.jpg) Fix Chrome Too Many Requests 429 Error [Solved]22 outubro 2024
Fix Chrome Too Many Requests 429 Error [Solved]22 outubro 2024 -
ArcGIS Online Error message: Unable to load https: - Esri Community22 outubro 2024
-
 Google update: Curious about disappearing Chrome extensions? Google's new update has all the answers - The Economic Times22 outubro 2024
Google update: Curious about disappearing Chrome extensions? Google's new update has all the answers - The Economic Times22 outubro 2024 -
 How To Fix “Blocked due to other 4xx issue” error in GSC22 outubro 2024
How To Fix “Blocked due to other 4xx issue” error in GSC22 outubro 2024 -
 429 HTTP Response Status Code Definition: Example, Usage, Methods - Holistic SEO22 outubro 2024
429 HTTP Response Status Code Definition: Example, Usage, Methods - Holistic SEO22 outubro 2024 -
 How to Fix 429 Too Many Requests Error Code: 6 Methods22 outubro 2024
How to Fix 429 Too Many Requests Error Code: 6 Methods22 outubro 2024 -
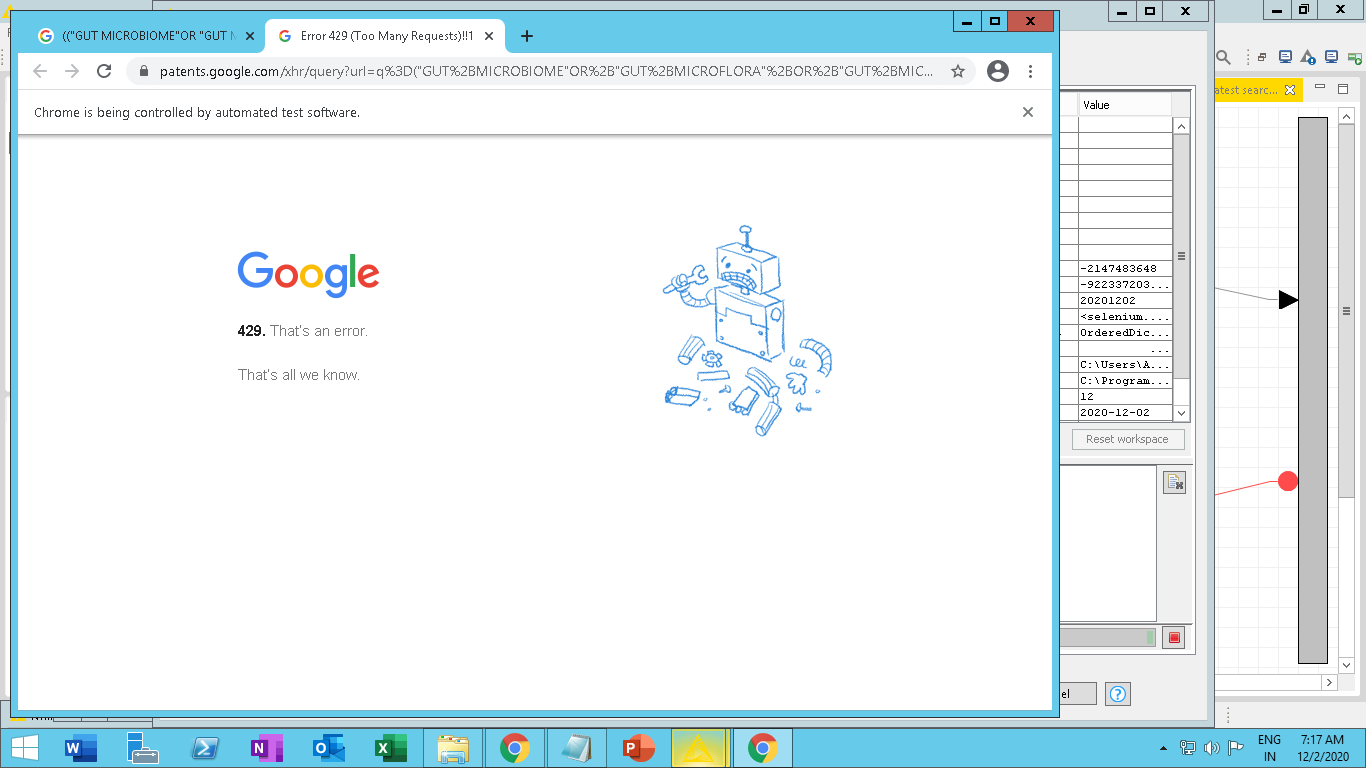 Too many requests error 429 while using python script node with22 outubro 2024
Too many requests error 429 while using python script node with22 outubro 2024 -
 Intermittent HTTP 429 Error when attempting to connect : r22 outubro 2024
Intermittent HTTP 429 Error when attempting to connect : r22 outubro 2024
você pode gostar
-
 Dragon Ball Legends Codes: How to Scan Dragon Ball Legends QR Codes22 outubro 2024
Dragon Ball Legends Codes: How to Scan Dragon Ball Legends QR Codes22 outubro 2024 -
Did Jiraiya know Sasuke was going to be a Good Guy in the original Naruto because of Boruto Episide 128? - Quora22 outubro 2024
-
 Reddit - Dive into anything22 outubro 2024
Reddit - Dive into anything22 outubro 2024 -
 BanG Dream! Morfonica Anime Reveals Title, Teaser Video, July 28-29 Premiere - News - Anime News Network22 outubro 2024
BanG Dream! Morfonica Anime Reveals Title, Teaser Video, July 28-29 Premiere - News - Anime News Network22 outubro 2024 -
 Car Crash Star - 🕹️ Online Game22 outubro 2024
Car Crash Star - 🕹️ Online Game22 outubro 2024 -
 Pokémon 3: O Feitiço dos Unown22 outubro 2024
Pokémon 3: O Feitiço dos Unown22 outubro 2024 -
 Christina Perri – A Thousand Years (Letra e Tradução) - MusicaTube22 outubro 2024
Christina Perri – A Thousand Years (Letra e Tradução) - MusicaTube22 outubro 2024 -
 Os 8 melhores jogos de simulação de vida - Canaltech22 outubro 2024
Os 8 melhores jogos de simulação de vida - Canaltech22 outubro 2024 -
 Stream Splix music Listen to songs, albums, playlists for free22 outubro 2024
Stream Splix music Listen to songs, albums, playlists for free22 outubro 2024 -
 App Store vs Google Play Store: Which One Is Better - MiniTool22 outubro 2024
App Store vs Google Play Store: Which One Is Better - MiniTool22 outubro 2024