Don't Cry Wolf: Tracking Dyre Wolf's Evolution - OPSWAT
Por um escritor misterioso
Last updated 01 novembro 2024

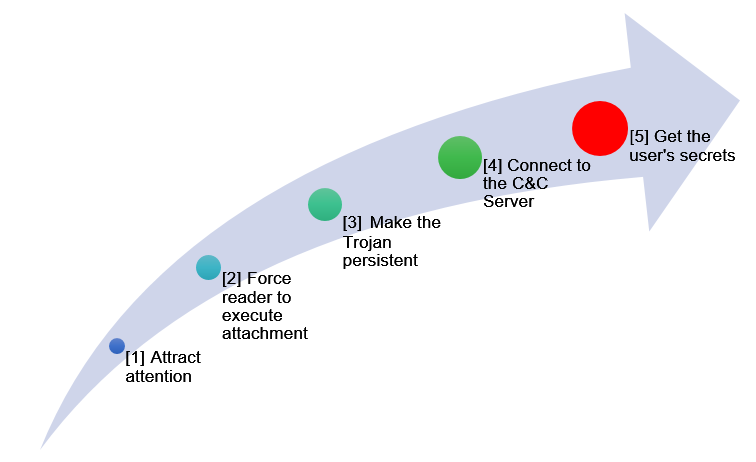
Few Trojans, however, have gained the level of notoriety and worldwide attention of Dyre, a piece of malware that relies heavily on social engineering to launch attacks. What makes this particular piece of malware troubling is the complexity of social engineering involved in the attack; the attack is multi-faceted, with rapidly evolving evasion techniques, and unlike many banking Trojans that target individual users, Dyre targets banking institutions as a whole! In this article we will explore the evolution of this particular piece of malware, how the attack has been so successful, and what can be done to eliminate this threat from your environment. IBM researches even credit the Dyre Trojan as the top malware offender for Q1 of 2015. In order for Dyre Wolf to socially engineer millions of dollars out of financial institutions, the malware must discover and take avenues that allow the threat to position itself onto a host, unbeknownst to the user. In early 2015 Trend Micro Labs identified two new evasion techniques of this piece of malware: Usage of SSL protocol to hide data being transmitted to and from the Command and Control Servers (C&C) Using a 12P address to mask the location of the CnC Server Dyre Attack Process: Fast forward to April of this year and the research and intelligence report done by IBM's Managed Security Services and Emergency Response Services and the malware has evolved several times more, introducing DDoS attacks and extremely advanced social engineering to bypass 2 factor form authentications. So how does this attack work? Image Courtesy of IBM Security 1) Spear Phishing The attack vector is a simple email attachment, encouraging the recipient to open the attachment and download the file within. Typically inside the zipped attachment is a file masquerading as a PDF, but is actually a .EXE or .SCR file. To the human eye the file looks exactly like a PDF and to make things worse the default Windows Behavior is to hide the extension of known files! 2) First Stage Malware Executed The file perpetrating as a PDF is a malware known as Upatre (pronounced like "Up a tree") The sole purpose of this malware is to download the Dyre The malware contacts checkup.dynds,org to determine the public IP address of the endpoint it has found itself on After confirming access to the internet, Upatre reaches out to the C&C server and downloads the malware from a varied list of domains and changing file names. 3) Second Stage Malware Executed Once the Dyre is downloaded Upatre removes itself, and all actions past this point are done via Dyre, which then runs a series of different steps to remain concealed to the host/victim: As a part of the installation service, Dyre creates a service named Google Update Service, it is set to run every time the system restarts. Once restarted Dyre injects malicious code into SVCHOST.EXE, stopping the Google Update Service Dyre makes multiple connections to 12P nodes to create a peer-to-peer tunneling network. Masking what and where information is being sent to Past that point Dyre hooks into the victims browsers, listening in to any credentials entered to visit a targeted bank's site If Dyre detects Outlook is installed, it will look to send emails with the Dyre payload to contacts in order to create a bot farm of diseased endpoints 4) Victim tries to log into a targeted banking account Dyre monitors the activity of the compromised endpoint, and the second the user navigates to the targeted banking site, the malware will redirect the request through a proxy server over to Dyre's server. The user will be shown a fake replica of the Bank's site and be prompted to fill in information used to steal money out of the account 5) The Phone Call In advanced variants of the attack, users are told to dial into a number to speak with what they believe to be a bank employee. In reality they are speaking to a member of this hacker ring and find themselves willingly handing over PII that can be used to bypass 2 form factor authentication. 6) The Wire Transfer Once all the necessary information is co

まとめ スティーヴ・ミラー・バンド 名盤 レア - 洋楽

Direwolf - ARK: Survival Evolved Wiki

Attack Animal: Wolf in Characters - UE Marketplace

Nowheres Wolf - Meet our OR-7 wolf 🐺 #stopmotion #puppet . Oregon

Tracking Error: Who is QDOT Chya??

dire wolf sightings|TikTok Search

Evolution: Devastator Warzone

WOLF DEVIL - THE DANGOROUS PISTOL - HARDCORE WORLDWIDE (OFFICIAL

Dire Wolf - Official 7 Days to Die Wiki

Wolfspell Records

Dire Wolf, Cryptid Wiki

Online:Vicious Dire Wolf - The Unofficial Elder Scrolls Pages (UESP)
Recomendado para você
-
IKARUS mobile.security - Apps on Google Play01 novembro 2024
-
Contains Ikarus trojan · Issue #165 · cDima/Aerial · GitHub01 novembro 2024
-
 Help me - Malware Finding and Cleaning - ESET Security Forum01 novembro 2024
Help me - Malware Finding and Cleaning - ESET Security Forum01 novembro 2024 -
 Trojan IT Security Matters01 novembro 2024
Trojan IT Security Matters01 novembro 2024 -
 Trojan Minibus. Commercial vehicle, Bus coach, Trojan01 novembro 2024
Trojan Minibus. Commercial vehicle, Bus coach, Trojan01 novembro 2024 -
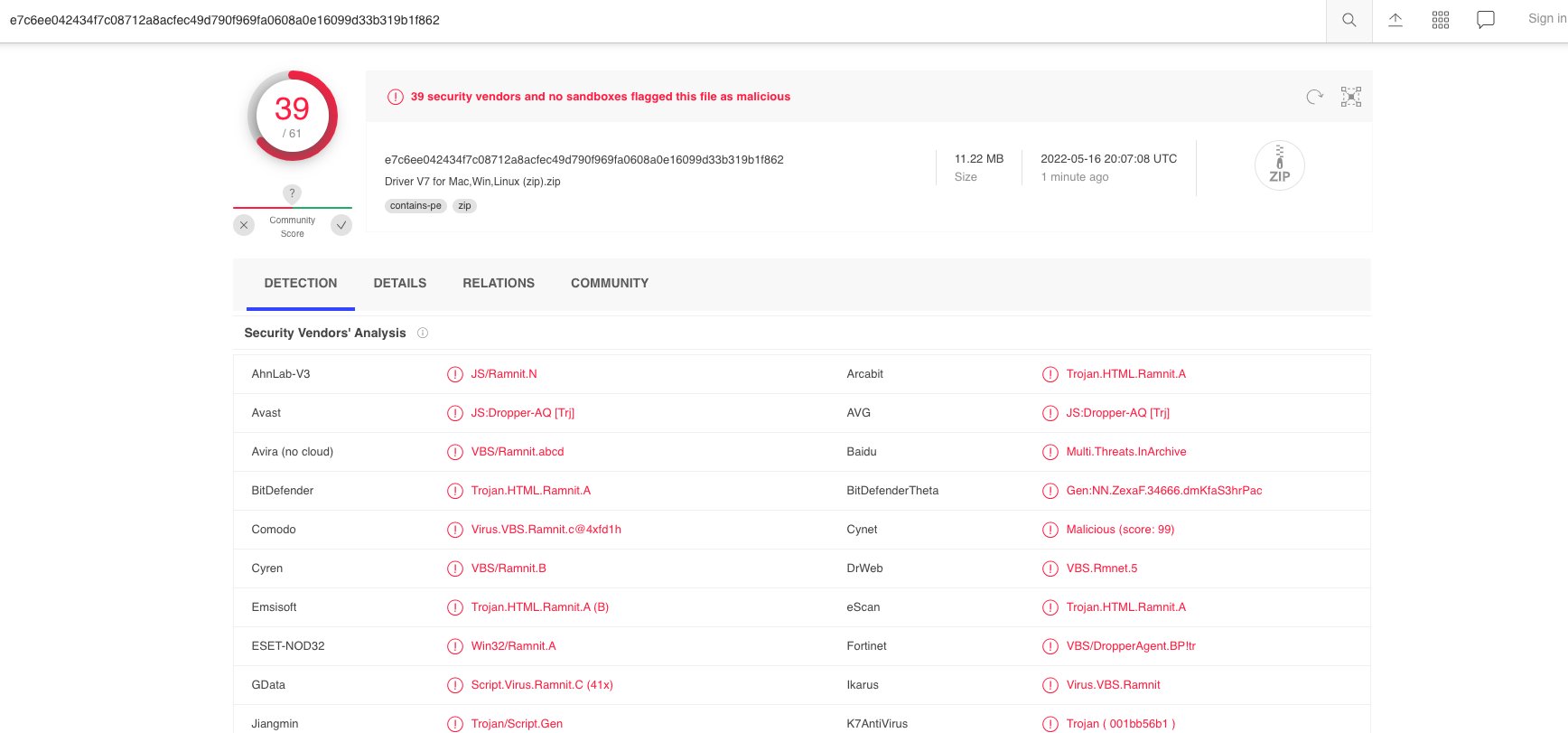 briankrebs on X: 3/ And then you think, hrm.maybe I should scan this thing at Virustotal, just because who TF is this company anyway? Holy smokes! 39 different antivirus tools detect this01 novembro 2024
briankrebs on X: 3/ And then you think, hrm.maybe I should scan this thing at Virustotal, just because who TF is this company anyway? Holy smokes! 39 different antivirus tools detect this01 novembro 2024 -
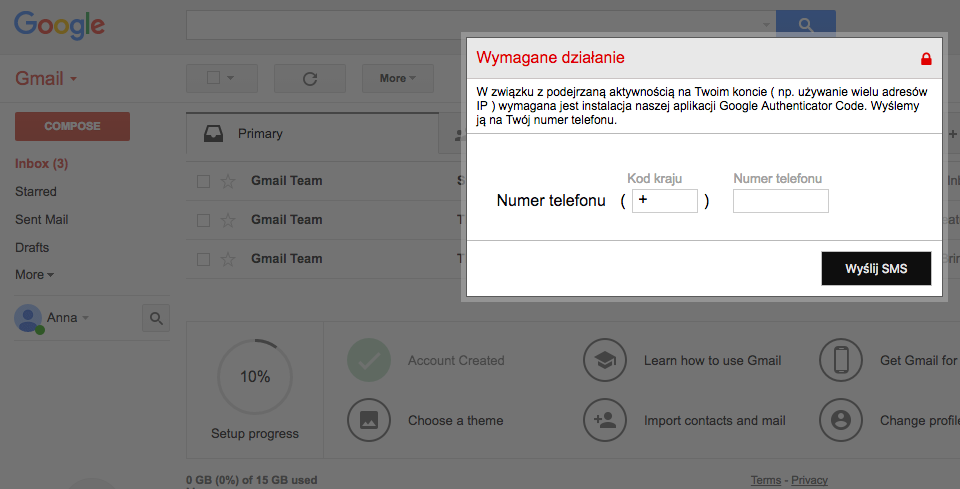 Banking trojan, Gmail webinject, SMS message and malicious APK – all in one attack scenario – BadCyber01 novembro 2024
Banking trojan, Gmail webinject, SMS message and malicious APK – all in one attack scenario – BadCyber01 novembro 2024 -
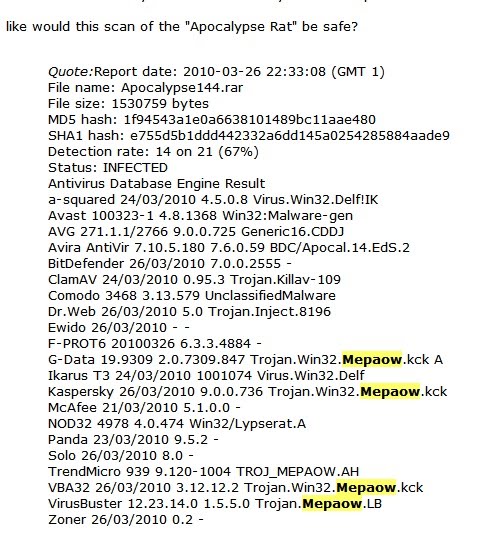 contagio: Apr 18 Malware Links Win32.Mepaow - RAT (Apocalypse RAT?)01 novembro 2024
contagio: Apr 18 Malware Links Win32.Mepaow - RAT (Apocalypse RAT?)01 novembro 2024 -
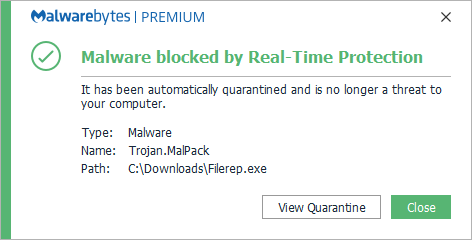 Trojan.Malpack01 novembro 2024
Trojan.Malpack01 novembro 2024 -
![PDF] Analysing web-based malware behaviour through client honeypots](https://d3i71xaburhd42.cloudfront.net/16a19e59aa8694dbc45be22e6dc3b2ca47b8fc85/122-Figure7-8-1.png) PDF] Analysing web-based malware behaviour through client honeypots01 novembro 2024
PDF] Analysing web-based malware behaviour through client honeypots01 novembro 2024
você pode gostar
-
 Peppa Pig Português Brasil, Poças De Lama, HD01 novembro 2024
Peppa Pig Português Brasil, Poças De Lama, HD01 novembro 2024 -
 MIAMI BEACH, FL - FEBRUARY 2016: Apple Store entrance at night in Lincoln Road Stock Photo01 novembro 2024
MIAMI BEACH, FL - FEBRUARY 2016: Apple Store entrance at night in Lincoln Road Stock Photo01 novembro 2024 -
 Buster Douglas Devastated By His Mother's Death Right Before the01 novembro 2024
Buster Douglas Devastated By His Mother's Death Right Before the01 novembro 2024 -
 Play Online Stay Connected01 novembro 2024
Play Online Stay Connected01 novembro 2024 -
 Shadow The Hedgehog ROM Download - Nintendo GameCube(GameCube)01 novembro 2024
Shadow The Hedgehog ROM Download - Nintendo GameCube(GameCube)01 novembro 2024 -
SPEEDRUN Hollow Knight #hollowknight #anyradiance #speedrun #hollowkni01 novembro 2024
-
 Jogo de luta Stickman fighting versão móvel andróide iOS apk baixar gratuitamente-TapTap01 novembro 2024
Jogo de luta Stickman fighting versão móvel andróide iOS apk baixar gratuitamente-TapTap01 novembro 2024 -
 Ghost Condemned Operator Simon Riley Mask - Call of Duty - Modern Warfare 2 - WARZONE - STL model 3D print file01 novembro 2024
Ghost Condemned Operator Simon Riley Mask - Call of Duty - Modern Warfare 2 - WARZONE - STL model 3D print file01 novembro 2024 -
 Desperados Exotiqa” by WeWantMore for Heineken - World Brand Design Society01 novembro 2024
Desperados Exotiqa” by WeWantMore for Heineken - World Brand Design Society01 novembro 2024 -
Truco Blyts – Apps no Google Play01 novembro 2024
